⚡Key Takeaways
- A multi-tenant cloud lets multiple customers share the same infrastructure without sharing data. It’s the architectural foundation behind most modern SaaS platforms because it balances scalability, cost efficiency, and speed.
- The real complexity is the product behavior. Multi-tenancy affects security models, analytics, permissions, reporting, and customer trust far beyond hosting.
- Done right, multi-tenancy accelerates growth. Done poorly, it multiplies risk. Isolation, governance, and tenant-aware analytics are the difference.
- Platforms like Qrvey reduce the operational burden by handling tenant-aware analytics, permissions, and reporting so SaaS teams don’t have to custom-build everything themselves.
Multi-tenancy sounds simple on paper. One platform. Shared infrastructure. Clean separation between customers. Done.
In practice, it’s rarely that neat. The architectural choices you make early on quietly shape everything that follows: how permissions work, how analytics are delivered, how trust is maintained as your customer base grows.
A multi-tenant cloud can be a powerful foundation for SaaS, but only if it’s designed with the downstream implications in mind.
In this guide, we’ll walk you through how multi-tenant cloud architecture works, why teams choose it, and where things tend to get complicated.
What Is a Multi-Tenant Cloud?
A multi-tenant cloud is an architecture where one instance of a software application serves multiple customers, with each customer operating in a logically isolated environment.
Every tenant:
- Shares the same codebase
- Runs on shared infrastructure
- Has isolated data, configurations, and access controls
Think of it like an apartment building. Everyone shares the same structure, utilities, and maintenance, but each tenant has their own unit.
Many SaaS companies prefer this model because it enables faster updates, easier maintenance, and significantly lowers operational overhead compared to managing separate environments for each customer.
Importantly, multi-tenancy is not inherently insecure. When designed correctly, tenant data is isolated through strong access controls, logical partitioning, and policy enforcement, not physical separation.
Multi-Tenant vs. Single-Tenant Cloud: Key Differences
Single-tenant and multi-tenant architectures solve very different problems. Neither is universally “better”. The right choice depends on scale, cost structure, and product complexity.
| Factor | Single-tenant cloud | Multi-tenant cloud |
|---|---|---|
| Infrastructure | One environment per customer | Shared environment across customers |
| Cost | Higher (duplicated resources) | Lower (shared resources) |
| Scalability | Slower, manual | Built-in, elastic |
| Customization | Easier for one-offs | Requires stronger design discipline |
| Maintenance | Per-customer overhead | Centralized updates |
| Analytics complexity | Simpler at small scale | Requires tenant-aware design |
At a high level, the difference between multi-tenant and single-tenant cloud comes down to how infrastructure and resources are shared, and who controls them.
A multi-tenant cloud is typically preferred by SaaS companies that need to scale efficiently, keep costs predictable, and deliver frequent updates across a growing customer base.
By contrast, a single-tenant cloud is often favored by teams with strict regulatory requirements, highly customized deployments, or customers who are willing to pay more in exchange for isolation and control.
How Multi-Tenant Cloud Architecture Works
Multi-tenant SaaS architecture relies on logical isolation, not physical separation. One application and infrastructure stack serves many customers, but everything a user sees or does is filtered through their tenant context.
Behind the scenes, this usually includes a shared application layer with one codebase, tenant-aware data models that associate records with a specific tenant, and strict access controls to ensure users only see what they’re authorized to access. And tenant-specific configuration allows branding, permissions, features, and analytics to vary by customer.
This is where many SaaS teams start to feel friction. Sharing infrastructure is relatively straightforward; it’s much harder to ensure dashboards, reports, and exports consistently respect tenant boundaries.
Embedded analytics platforms help by enforcing that isolation automatically, allowing SaaS teams to deliver self-service analytics in multi-tenant environments, without piling on fragile, custom logic that becomes hard to maintain over time.
Take a peek at how to set up Record Level Security with Qrvey in this clickable demo.
Benefits and Security Risks of Multitenancy
Multi-tenancy is a balancing act. We usually see the benefits first while the risks surface more gradually as the platform grows.
For most SaaS teams, it’s the only model that makes growth realistic. But as the customer base expands, small mistakes carry more weight. A permissions gap or missed filter doesn’t stay isolated; it affects more than one customer.
| Area | What Works Well | Where Risk Shows Up |
|---|---|---|
| Infrastructure | Lower costs | Performance contention |
| Operations | Faster updates | Errors scale quickly |
| Security | Centralized controls | Data exposure if isolation breaks |
| Analytics | Shared reporting | Tenant boundaries easy to miss |
Benefits
1. Cost efficiency at scale
When we talk to SaaS teams about multi-tenancy, the first benefit they mention is cost. It’s the one you feel immediately. Instead of spinning up separate infrastructure for every customer, you’re sharing the heavy stuff (compute, storage, networking) across tenants and using software controls to keep data isolated.
That pooled model makes growth financially realistic, especially once you’re supporting lots of mid-sized customers instead of a handful of whales.
The cost win is real, as long as isolation is designed correctly from day one.
2. Faster product iteration
This is the second benefit we see teams fall in love with: you ship once and everyone gets it.
With multi-tenancy, you’re not coordinating upgrades across dozens (or hundreds) of customer-specific deployments. You’re maintaining one core platform, which makes it much easier to roll out improvements, fix bugs, and keep security patches consistent.
Over time, that simplicity becomes a competitive advantage because your release process stays predictable instead of turning into a customer-by-customer negotiation.
It also helps internally. Support and engineering don’t have to remember “which tenant is on which version.” Product doesn’t have to delay features because a subset of customers can’t upgrade.
3. Centralized controls for better security
Done well, multi-tenancy can make security more consistent across customers: one permission model, one set of enforcement points, one place to monitor and harden.
Customers care that isolation is enforced everywhere: in the app, in exports, in dashboards, in reporting, and in edge cases you only discover months later. When the security model is unified, it’s easier to prove and maintain that consistency.
The caveat is obvious: if your tenant context isn’t enforced everywhere, centralization becomes a single blast radius, which is why teams need to treat isolation as foundational.
Take a peek at how to set up Record Level Security with Qrvey in this clickable demo.
4. Easier SaaS analytics enablement
If your SaaS product includes analytics, multi-tenancy can be a real unlock. You’re building one reporting experience that can serve every tenant.
Where we see teams struggle is the amount of work it takes to keep analytics tenant-aware as complexity grows: roles, permissions, data models, and self-service requests all add pressure.
That’s why many SaaS teams look at embedded analytics platforms as a force multiplier: not to outsource thinking, but to reduce the fragile custom logic that tends to break isolation over time. The goal is a scalable, tenant-safe reporting experience customers can trust beyond fancy dashboards.
This is where platforms like Qrvey eliminate heavy lifting by handling tenant isolation, reporting logic, and embedded analytics securely.
Challenges
1. Performance contention
The tradeoff of shared infrastructure is shared impact. When tenants run on the same underlying resources, one tenant’s spike can become everyone else’s slowdown – if you don’t plan for it.
We’ve seen teams underestimate this early because performance is “fine” at low scale, and then suddenly you onboard a tenant with heavier workloads, bigger datasets, more frequent reporting, or aggressive exports, and your platform starts behaving unpredictably.
2. Errors scale quickly
In multi-tenancy, a mistake rarely stays contained.
A misconfiguration, a deployment bug, a permission regression can impact multiple tenants at once because everyone is riding the same platform. This changes the way teams need to operate. You need stronger release discipline, safer defaults, better testing around tenant context, and clearer rollback paths.
The teams that thrive in multi-tenancy treat operations as a product capability: predictable releases, good observability, and automation everywhere it’s practical.

3. Data isolation failures become the trust breaker
The biggest fear SaaS leaders have with multi-tenancy is accidental data exposure. Even one mistake in permissions, joins, or filters can erode trust beyond repair.
Here’s a practical takeaway: enforce tenant context everywhere, and assume analytics/reporting surfaces are high-risk because they touch data broadly. Once trust is damaged, it’s hard to win back, so isolation needs to be engineered as a non-negotiable baseline, not as a feature.
4. Tenant boundaries are easy to miss, especially with self-service
Most teams are good about tenant isolation in the core app because it’s part of everyday feature development. But analytics tends to live slightly off to the side and that’s where boundaries get missed.
We’ve seen teams rely on “we’ll just filter by tenant ID” approaches, and that works, until someone adds a join, a new dataset, or a self-service capability that bypasses the usual guardrails.
Self-service makes this harder, not easier. The whole point is giving users flexibility, and flexibility can accidentally expose edge cases where tenant context isn’t enforced consistently.
Pro tip: The fix isn’t to avoid self-service; it’s to make tenant enforcement automatic.
VIDEO: Multi-Tenant Security in SaaS: Risk, Architecture & What to Evaluate
Best Practices for Multi-Tenant Cloud Architectures
Teams that do this well design for isolation, analytics, and governance from the start.
In our experience, the biggest gains come from enforcing tenant boundaries everywhere, avoiding custom logic, and automating the parts that tend to break as usage grows. These practices are what we’ve consistently seen hold up over time, especially for SaaS platforms delivering customer-facing analytics.
Practice #1: Enforce tenant isolation everywhere, not just where it’s obvious
Tenant isolation can’t live in just one layer of the stack. The most common failures we see come from edge cases: places where tenant context was assumed, not enforced.
Our rule of thumb is to make isolation automatic. Every request should carry tenant context, and every data interaction should respect it by default. If developers have to remember to add checks manually, something will eventually slip through.
This becomes especially risky in analytics, where queries are broader and more flexible. Teams that examine different data‑security models for multi‑tenant analytics usually reach the same conclusion we have: platform‑level enforcement is far more reliable than scattered, custom rules.
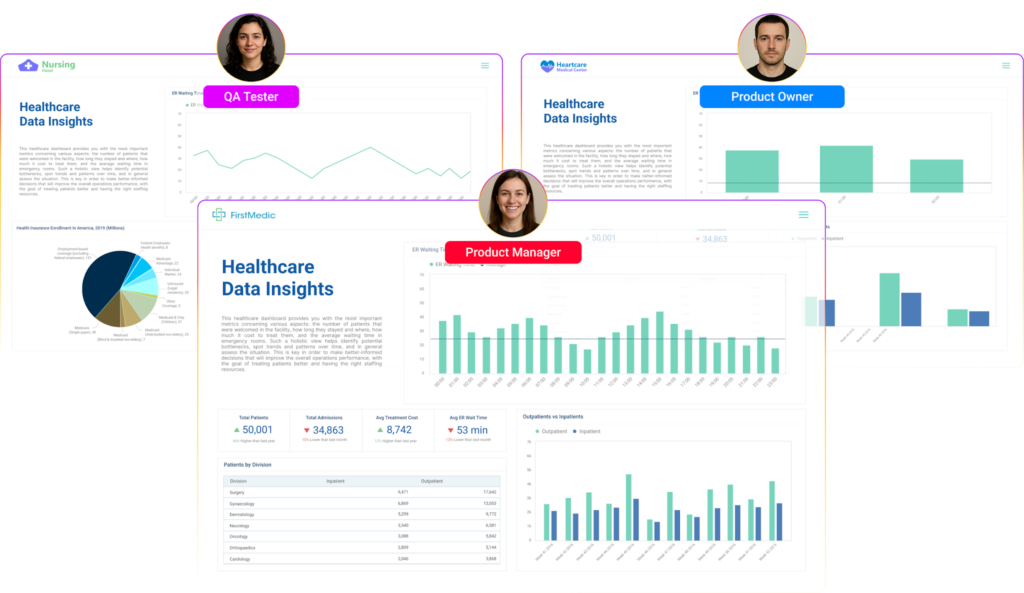
Practice #2: Treat analytics as a first‑class multi‑tenant concern
Some SaaS teams bolt on analytics after a product is already multi-tenant. That’s usually when problems start. Dashboards may work, but permissions don’t quite line up. Self‑service features bypass guardrails. Export paths behave differently than in‑app views.
We’ve found it’s better to assume analytics will be one of the hardest places to maintain isolation and design accordingly. That means choosing tools and patterns that are tenant-aware by design, not patched together later.
This is why so many SaaS teams evaluate embedded analytics platforms instead of general-purpose BI tools. They need dashboards, reports, and self‑service experiences that automatically respect tenant and user boundaries. General-purpose BI tools are not designed for this.
The goal is to prevent analytics from becoming the weak link in an otherwise solid multi-tenant system.
Practice #3: Automate data workflows before manual work piles up
In a multi-tenant environment, manual data work scales badly. We’ve seen teams spend more time onboarding tenants, syncing data, fixing reports, and managing exports than improving the product. Those tasks start small, but they add up fast.
Automating data workflows early helps avoid that trap. When ingestion, transformation, reporting, and refresh processes are standardized, teams spend less time firefighting and more time building.
See how to build an automation workflow with Qrvey in this clickable demo.
This matters even more in multi-tenant systems, where the same workflow needs to run reliably across many customers. Tools that support data workflow automation can significantly reduce operational overhead while keeping tenant data cleanly separated.
For us, automation is about making sure scale doesn’t introduce avoidable instability.
Practice #4: Design for scale before performance forces your hand
Performance problems in multi-tenant systems emerge gradually as usage patterns change. One tenant grows faster than expected. Another runs heavier reports. Suddenly, shared resources start to feel tight.
Teams that handle this well plan ahead. They monitor usage closely, anticipate noisy‑neighbor scenarios, and design data access patterns that can scale without constant rework.
This often ties back to data architecture choices: how datasets are structured, when separation makes sense, and how data lakes are built without turning governance into a mess.
Performance issues are far easier to prevent than to fix once customers are already feeling the impact.
On-demand Webinar : How to Succeed with Multi-Tenant Analytics
Multi-Tenant Cloud Examples & Use Cases
Multi‑tenant cloud architecture tends to get tested at very specific moments as a SaaS product grows. Below are examples reflecting situations we’ve consistently seen force real architectural decisions, especially once customer-facing analytics and reporting are in scope.
Example 1: Scaling customer analytics beyond the first 50-100 tenants
- Early analytics often rely on simple tenant filters
- Dashboards work fine until customers ask for exports, customization, or deeper access
- Role-based visibility inside a single tenant adds another layer of complexity
This is one of the first places multi-tenancy starts to strain. We’ve seen teams ship analytics quickly, only to realize later that reporting paths bypass application-level safeguards. What looked safe at low scale starts to feel risky as usage grows.
At this stage, many teams move away from custom analytics logic and toward embedded analytics platforms like Qrvey that enforce tenant boundaries automatically across dashboards, reports, and exports, without relying on every query being written perfectly.
Example 2: Supporting different data maturity levels on the same platform
- Some tenants want simple, fixed dashboards
- Others expect self-service analytics and deeper exploration
- Enterprise customers demand tighter governance and auditability
Multi-tenancy is about supporting very different expectations on the same platform. We’ve seen SaaS teams struggle when analytics are designed for the “average” customer, leaving advanced users frustrated and less mature users overwhelmed.
The challenge is providing flexibility without creating tenant-specific logic that becomes impossible to maintain.
Teams that handle this well standardize their analytics foundation while letting experiences vary by role and tenant maturity, often using embedded analytics to keep governance consistent without blocking growth.
Example 3: Introducing self-service reporting without expanding risk
- Self-service reduces support requests
- Users can build dashboards, combine datasets, and export data
- Tenant and role boundaries are suddenly under more pressure
Self-service is where multi-tenant risk expands fast. We’ve seen teams confidently roll it out, only to discover later that tenant isolation wasn’t enforced consistently across all analytics paths.
A missed filter or permission gap doesn’t stay contained; it affects more than one customer. This is why many SaaS teams rethink analytics architecture before (or shortly after) enabling self-service.
Platforms like Qrvey make this easier to implement securely at scale by enforcing tenant boundaries by design, rather than relying on fragile custom logic.
Take a peek at Qrvey’s self-service capabilities in this clickable demo.
Where Qrvey Fits
After thousands of multi-tenant analytics deployments with SaaS teams, we’ve seen the same issue come up repeatedly: the infrastructure scales, but analytics and reporting become harder to manage without adding risk.
Tenant boundaries get blurry, permissions grow complex, and teams end up maintaining fragile custom logic just to keep analytics secure and reliable.
This is where Qrvey fits naturally.
Rather than treating analytics as a bolt‑on, Qrvey is designed to operate as a tenant‑aware, embedded analytics solution, enforcing isolation, roles, and permissions by default.
It helps teams deliver dashboards, reports, and self‑service analytics without rebuilding tenant logic for every use case, while still supporting automation and data workflows as the platform grows.
If you’re evaluating how to scale customer‑facing analytics securely, a good next step is to explore Qrvey by booking a demo or exploring our interactive demo center.
FAQs:
- Are multi-tenant cloud services right for my platform?
If you’re serving multiple customers with shared functionality and need scalability, multi-tenancy is usually the right architectural choice.
- For single-tenant setups, does Qrvey favor per-tenant connections or per-tenant datasets?
For a single tenant setup, Qrvey favors the “per-tenant dataset” method. If it is necessary to keep tenant data isolated, then the easiest thing to do is to create a connection that connects to a specific tenant’s database or schema, and then ingest the data into an isolated dataset.
- Can Qrvey push role-based personalizations programmatically at scale?
Yes, dashboard builders who belong to the primary SaaS organization can build role-based custom dashboards and deploy them to all tenant end users who have the matching role.
- How does Qrvey deploy the same dashboard to hundreds of tenants while preserving permissions?
Qrvey provides custom attribute properties that behave as “tags”, which can be used to tag specific dashboards with security access permission information. You can then use Qrvey’s Content Deployment feature to push these dashboards, along with their custom tags, to hundreds of tenant workspaces in production.

David is the Chief Technology Officer at Qrvey, the leading provider of embedded analytics software for B2B SaaS companies. With extensive experience in software development and a passion for innovation, David plays a pivotal role in helping companies successfully transition from traditional reporting features to highly customizable analytics experiences that delight SaaS end-users.
Drawing from his deep technical expertise and industry insights, David leads Qrvey’s engineering team in developing cutting-edge analytics solutions that empower product teams to seamlessly integrate robust data visualizations and interactive dashboards into their applications. His commitment to staying ahead of the curve ensures that Qrvey’s platform continuously evolves to meet the ever-changing needs of the SaaS industry.
David shares his wealth of knowledge and best practices on topics related to embedded analytics, data visualization, and the technical considerations involved in building data-driven SaaS products.
Popular Posts
Why is Multi-Tenant Analytics So Hard?
BLOG
Creating performant, secure, and scalable multi-tenant analytics requires overcoming steep engineering challenges that stretch the limits of...
How We Define Embedded Analytics
BLOG
Embedded analytics comes in many forms, but at Qrvey we focus exclusively on embedded analytics for SaaS applications. Discover the differences here...
White Labeling Your Analytics for Success
BLOG
When using third party analytics software you want it to blend in seamlessly to your application. Learn more on how and why this is important for user experience.